A computer network not only all allows the sharing of both hardware (Printer, Hard Drive, etc.) and software (files, folders, data, etc.) resources, but also enables the intercommunication between network nodes. Furthermore, a computer network consist of both front-end (Laptops, Desktops, Tablets, Printers, etc.) as well as bank-end (Switch, Hub, Router, Firewall, UPS, KVM, Blade Array, RAID, etc.) computer equipment. Most general computer users, although very familiar with front-end, are unfamiliar with with bank-end. This is ironic given that they interact with bank-end just as much as the front-end. Of course the more traditional name for back-end computer equipment is Network Hardware. For most general computer users their definition of Network Hardware would be a "Router" and Modem.
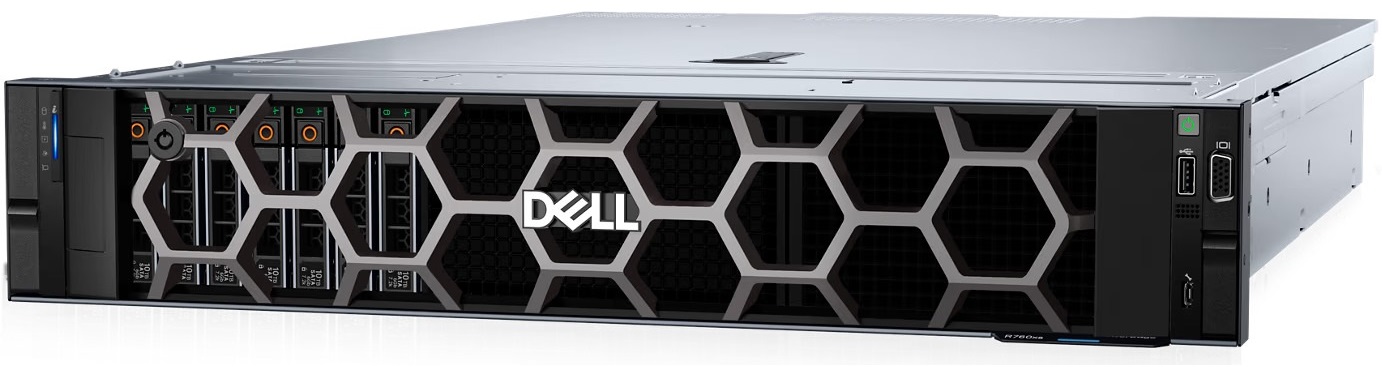
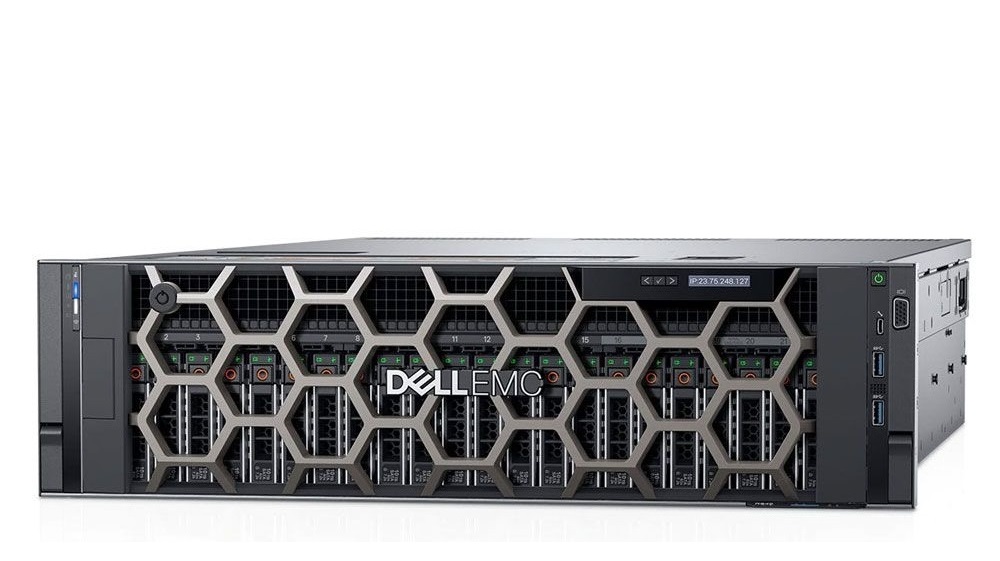
Rack Server
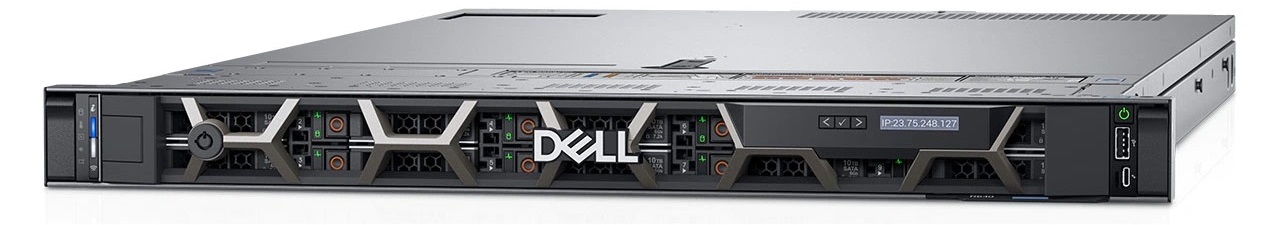
Rack Server Intro - All commercial grade computer networks have at least one Rack Server. Unsurprisingly, Rack Servers are designed specifically to be mounted on a Server Rack. A Rack Server is designed to execute not only the most demanding computer applications, but the most essential computer applications. Examples of demanding computer applications include Web-Server, Email Server, File Server, Firewall, etc. In every computer network the two most essential computer applications are Domain Name Server (DNS) and Dynamic Host Configuration Protocol (DHCP). No computer network just could not function without a DNS and DHCP.
General Definition - Non technical users shouldn't get intimidate by a Rack Server’s name or physical appearance. A Rack Server contains the same components, both hardware (CPU, RAM, Hard Drive, motherboard, etc.) and software (Operating System, Applications, Folders, Files, etc.), as a client computer. No only do all modern computers contain CPU, RAM, Hard Drive, those components dictate not only the cost of the computer, but also the performance. The only difference between a Rack Server and a general Client computer is that Rack Servers contain the latest and greatest technology, but the also contain more of it.

Technical Definition - The heart and soul of ALL computers lies in the CPU, RAM and Hard Drive. Examples of computers include but not limited to Laptops, Desktops, Rack Servers, Tablets, and yes even Rack Servers. It is hard, even for even the computer layman to be unacquainted with these components as consumers are constantly bombarded by them. For example, when purchasing a new computer, these specs are thrown at your face in hopes of enticing consumers to purchse the computer. Not only do all modern computers possess those three components, but they directly determine the cost of the computer but also the performance. A modern desktop computers typically has four core CPU, 8 Gigabytes of RAM and 500 Gigabytes of Hard Drive.
Rack Server vs PCs - A modern desktop computer typically has a four core CPU, 8 Gigabytes of RAM and 500 Gigabytes of Hard Drive. Conversely, a modern Rack Server has 32 Core CPU, 8 Terabytes of RAM and 100 Terabytes of Hard Drive.

Operating System - Like any other computer, a Rack Server computer requires an operating system to abstract the hardware from executing applications. Unlike a regular “client” computer which requires a client operating system, a Rack Server computer requires Server Operating System. Examples of Server Operating Systems include but not limited to Windows Server, Ubuntu Server, etc. Conversely, examples of Client Operating System include but not limited to Windows Home Edition, Ubuntu Maverick, etc.
Specific Definition - Affordably address common business workloads while delivering powerful compute with an entry-level 1U rack server.
- Processor - Intel® Pentium G6505 4.2GHz
- Memory - 1x 8GB, 3200MHz
- Hard Drive - 1x 1TB HD SATA